A few weeks ago, I wrote about why we need to stop blaming users for choosing dumb passwords: we’ve designed a system that’s basically impossible to use “correctly.”
It’s not all doom and gloom for authentication design, though. I’m heartened to see some new authentication patterns taking hold. Some are entirely new, inspired by the constraints and affordances of new devices. Some are variations on patterns that have been standard in particular industries but are now hitting the consumer market. Plenty of security experts have weighed in on the technical aspects of new authentication patterns, so let’s explore the user experience implications.
How do these emerging patterns stack up? I’ll look at these three criteria:
- Are they cognitively reasonable? This is where passwords fail: sign-in systems shouldn’t expect people to do things like remember long strings of random characters.
- Do they feel like the right level of security for the situation? Nobody wants to use a thumbprint in order to comment on Facebook.
- Are they practical in the expected context? It’s not sensible to use a voiceprint at a noisy DMV office.
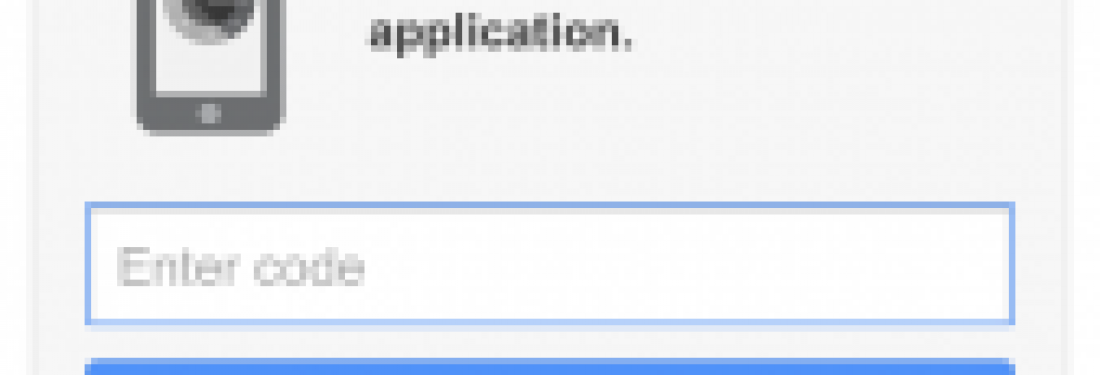
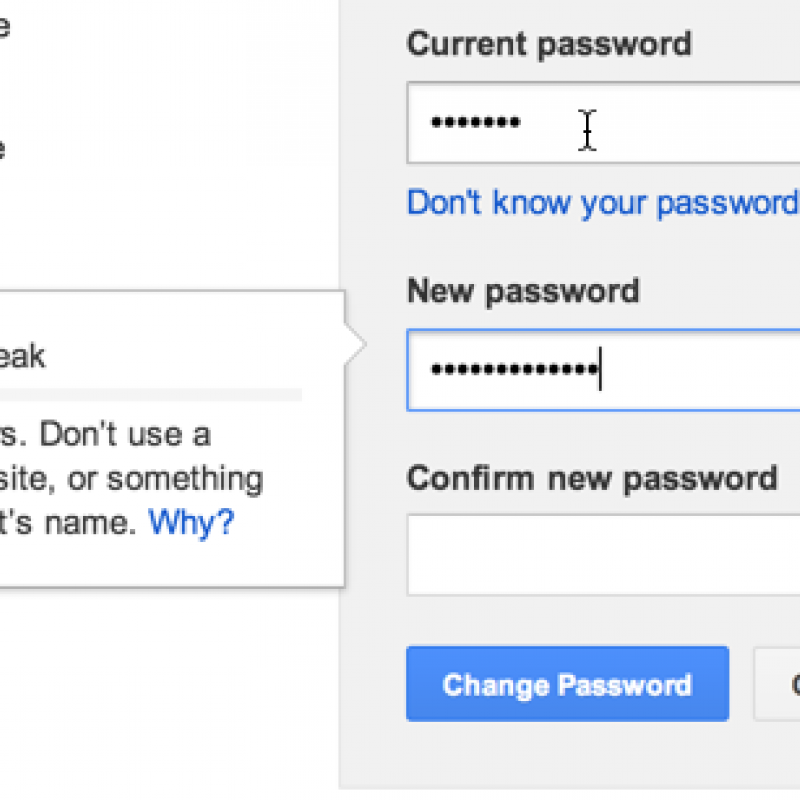
The extra layer: Two-factor authentication In two-factor authentication, users enter a code displayed on one device in addition to a password. This doesn’t replace passwords; it’s a second password, often on a different device.
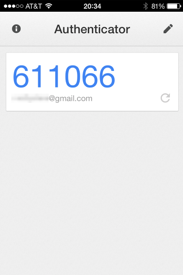
You can secure your Google accounts with an extra code, displayed on your phone.
- Cognitively reasonable? Sure. It’s an extra step, but nothing extra to remember.
- Feels like the right level of security for the situation? An extra layer of security is fine, as long as protecting the info feels worthwhile. Right now, two-factor authentication is mostly reserved for email and financial and medical information – and that’s a good thing.
- Practical in context? Sometimes. Often, when I’m checking my email at a public computer, I’m in a hurry, and the last thing I want to do is pull out my phone.
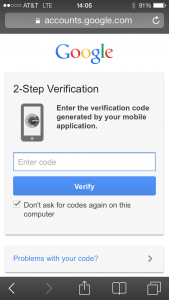
- Also, sometimes I want to access email from my phone – and the security code is also on my phone. Using your mobile device to sign onto your mobile device is clunky and doesn’t offer much security benefit.
- The bottom line: Save two-factor authentication for when it’s really and truly worth it.
The visual password: Gesture-based authentication Why type when you can swipe? These techniques let you authenticate with gestures on touchscreens instead of poking at tiny, limited keyboards.
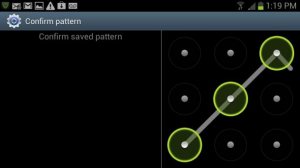
Source: cnet.com Unlocking an Android phone requires users to trace a pattern on a grid of 9 dots.

Source: Parity News
Windows 8 offers picture gesture authentication, where users choose a picture and then tap, drag, and “draw” a pattern on it; the picture and the pattern together serve as their password.
- Cognitively reasonable? For many people, tapping into spatial memory and muscle memory is a welcome change from remembering passwords.
- Feels like the right level of security for the situation? Images and patterns can be easier for a nosy onlooker to see and remember. Android’s 9-dot grid wouldn’t be appropriate at, say, an ATM.
- Practical in context? It’s easier and faster than typing a password on a mobile device, since the touch targets are larger.
- The bottom line: Best for frequently-repeated, on-the-go situations where people don't feel they're dealing with highly sensitive information directly.
- The password within you: Biometric authentication In biometric authentication, characteristics of your body serve as your credentials. On the one hand, it’s hard (though not impossible) to fake, and you'll never forget it. On the other hand, it’s impossible to change.
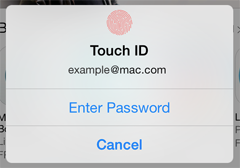
Source: Apple The iPhone 5S can unlock via a built-in fingerprint sensor.
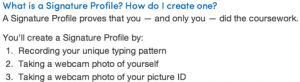
Source: Coursera
Coursera offers an interesting spin on biometric identification by using typing speed and rhythm as an auxiliary identifier. On a site where users are expecting to type a lot of text, asking them to type a sample paragraph wouldn’t stand out as inappropriate.
- Cognitively reasonable? Definitely. There’s absolutely nothing to remember; done right, biometrics can feel futuristically seamless.
- Feels like the right level of security for the situation? Maybe. Biometric authentication can easily feel intrusive and overly permanent. People won’t want all accounts inextricably linked to their real identities, and that’s okay.
- Practical in context? That depends. Designers need to be mindful of what it feels like to use biometric authentication in public, as well as whether the hardware is durable enough to filter out background noise, temperature, moisture, and other environmental factors. Also, biometrics’ permanence can backfire, as one blogger who cut his finger found out when his laptop would no longer recognize his fingerprint.
I had to turn off fingerprint scanning on my work laptop as it's too hot and it can't read properly. — annaleeanda (@annaleeanda) December 19, 2013
- Bottom line: Every step of the way, make sure people feel in control. One false step and biometric authentication gets creepy and obnoxious.
When you’re choosing and designing an authentication system, of course the security of people’s data is top priority. (Or at least it should be – ahem, Snapchat.) But don’t neglect design, and don’t forget about context. Keep in mind how, when, and why people are likely to need access. Don’t spend your time chasing seamless, space-age, and sexy. To keep people safe and sane, authentication needs to be, above all, appropriate.